On December 1, Polygon zkEVM began its audit. This audit represents an interesting challenge because it is meant to evaluate the security of a new kind of technology, specifically a technology designed to conceal information in a trustless way.
Given the nature of this challenge, we wanted to outline the methodology for the audit, its progress, and the next steps. We’ll also keep you updated with the progress of the audit and lessons learned in the coming weeks.
Today, Polygon zkEVM moves closer to a rollout on Ethereum’s Mainnet.
Defining Standards for zkEVM
Last month, Polygon collaborated with the Ethereum Foundation and other teams on a series of discussions about Zero Knowledge. There, a member of the Ethereum Foundation’s Privacy and Scaling Explorations team, described the task of an audit—any audit—as an attempt to verify the strongest explicit and implicit claim made by any given technology.
With that in mind, this audit is meant to verify the claim that Polygon zkEVM can only generate valid state transitions, and that it does so in a Zero Knowledge, non-interactive environment. The auditors of Polygon zkEVM are attempting to verify this claim across two vectors: correctness and soundness.
- Correctness means that honest entities can generate and validate state transitions.
- Soundness means that dishonest entities cannot generate a state transition is positively verified.
If a valid proof is verified and it generates a invalid state transition, that would be a correctness issue. If an invalid proof is verified, that would be a soundness issue.
Audit Methodology
Polygon zkEVM is being audited by two security firms, Spearbit and Hexens. An advantage of two auditing teams working independently is that the results each produces is made more robust in aggregate—Hexens’s feedback will be checked against Spearbit’s and vice versa.
The teams, which include key contributors to the Ethereum ecosystem, are performing their audits on the source code—the same source code that has been available since the public testnet was rolled out, in October. While the audit is expected to continue through January, the timeline for verifying the security of Polygon zkEVM is simple: As long as it takes.
Audit Scope
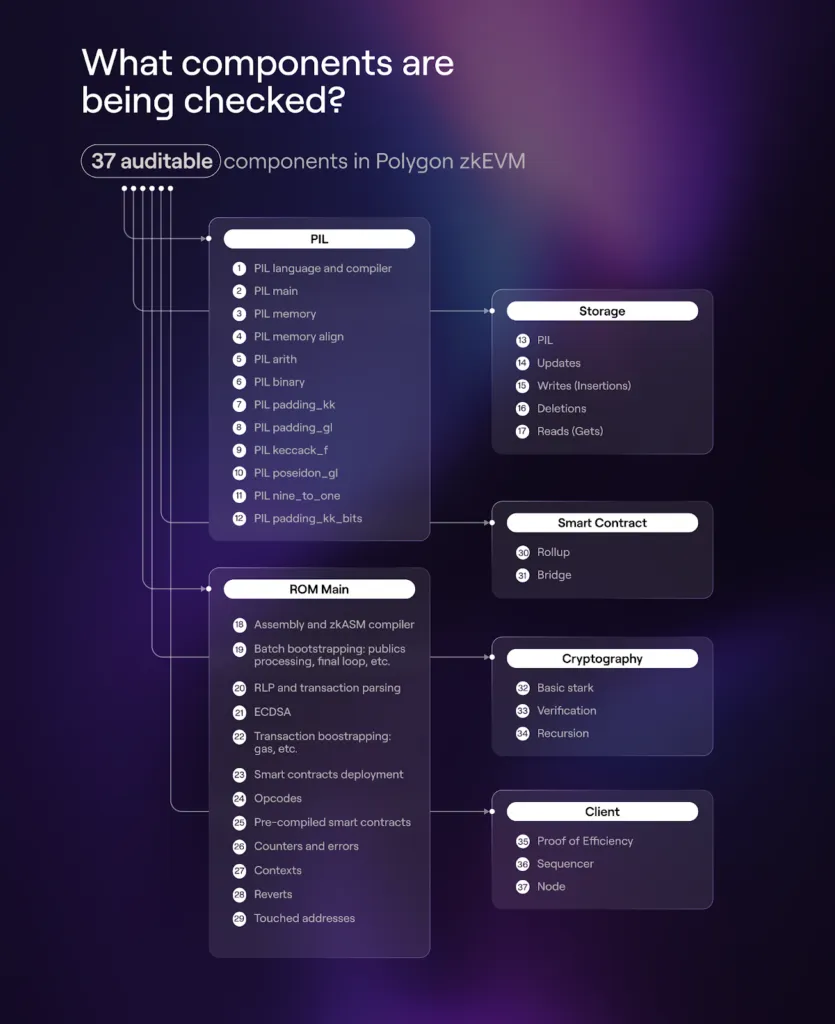
There are 37 auditable components in Polygon zkEVM. Every single one will be audited. Nothing is out of scope, and certainly not the smart contracts that verify the ZK proofs.
Let’s consider the process for generating one Zero Knowledge proof for one transaction to illustrate how these stacks fit together. The client stack includes the RPC node, sequencer and aggregator, which is where proofs are generated. Here, a subcomponent called the executor takes transactions as inputs and creates an execution trace matrix using instructions of a ROM program written in zkASM. This execution trace matrix is converted to a set of polynomials that must confirm equations defined in PIL. Once confirmed, a proof is generated. This proof guarantees that the state transition is correctly computed according to the set of transactions processed.
Polygon zkEVM was designed modularly, an unintended consequence of which is that it makes the task of auditing more efficient for both auditors and community members. And while no component is out of scope, the priority of each is partially a function of how much it overlaps with correctness and soundness.

In the coming weeks, Polygon zkEVM will be dramatically upgraded. Until now, Polygon zkEVM has been producing one proof per transaction. With the addition of recursion—which borrows concepts and design approaches from Polygon’s Zero team—Polygon zkEVM will begin generating proofs of proofs. (And proofs of proofs of proofs.) Adding recursion will give users the first real indications of throughput capacity.
Details on the implementation of recursion, along with improvements to Polygon zkEVM’s sequencer and the rollout of a new testnet will be available in the coming weeks—so stay tuned to our blog and social channels for the latest! If you want to read more about recursion right now, check out Plonky2: A Deep Dive.
Website | Twitter | Developer Twitter | Studios Twitter | Telegram | Reddit | Discord | Instagram | Facebook | LinkedIn













